Pause the Reserve agreement for eUSD and USD3 minting; the redemption function remains fully enabled

Reserve announced on the X platform on April 20 that, as the ABC Labs team is closely monitoring the Kelp DAO rsETH attack incident, it has temporarily paused eUSD and USD3 minting, rebalancing, and RSR redemption (unlock) operations. The redemption feature remains normally open. According to Reserve’s announcement, Reserve DTF holders are almost unaffected.
Reserve Protocol Suspension Measures and Risk Assessment
According to Reserve Protocol’s official announcement dated April 20, 2026, this precautionary measure covers: pausing eUSD minting, pausing USD3 minting, pausing rebalancing, and pausing RSR redemption (unlock); the redemption feature remains normally open. In the announcement, Reserve recommended that if users need RSR overcollateralization protection, they should continue holding.
Reserve’s announcement explains that if rsETH on the mainnet experiences a significant drop in value (estimated 15.5% to 18.5% loss), Aave may incur bad debt, which could then affect Aave V3’s USDC collateral. In the Reserve Protocol, USD3 and eUSD RSR stakers may play the role of a “first-loss capital” protection layer, but Reserve states the impact is extremely small, and RSR overcollateralization is sufficient to cover it.
Kelp DAO rsETH Attack: Timeline and Attack Mechanism
 (Source: GitHub)
(Source: GitHub)
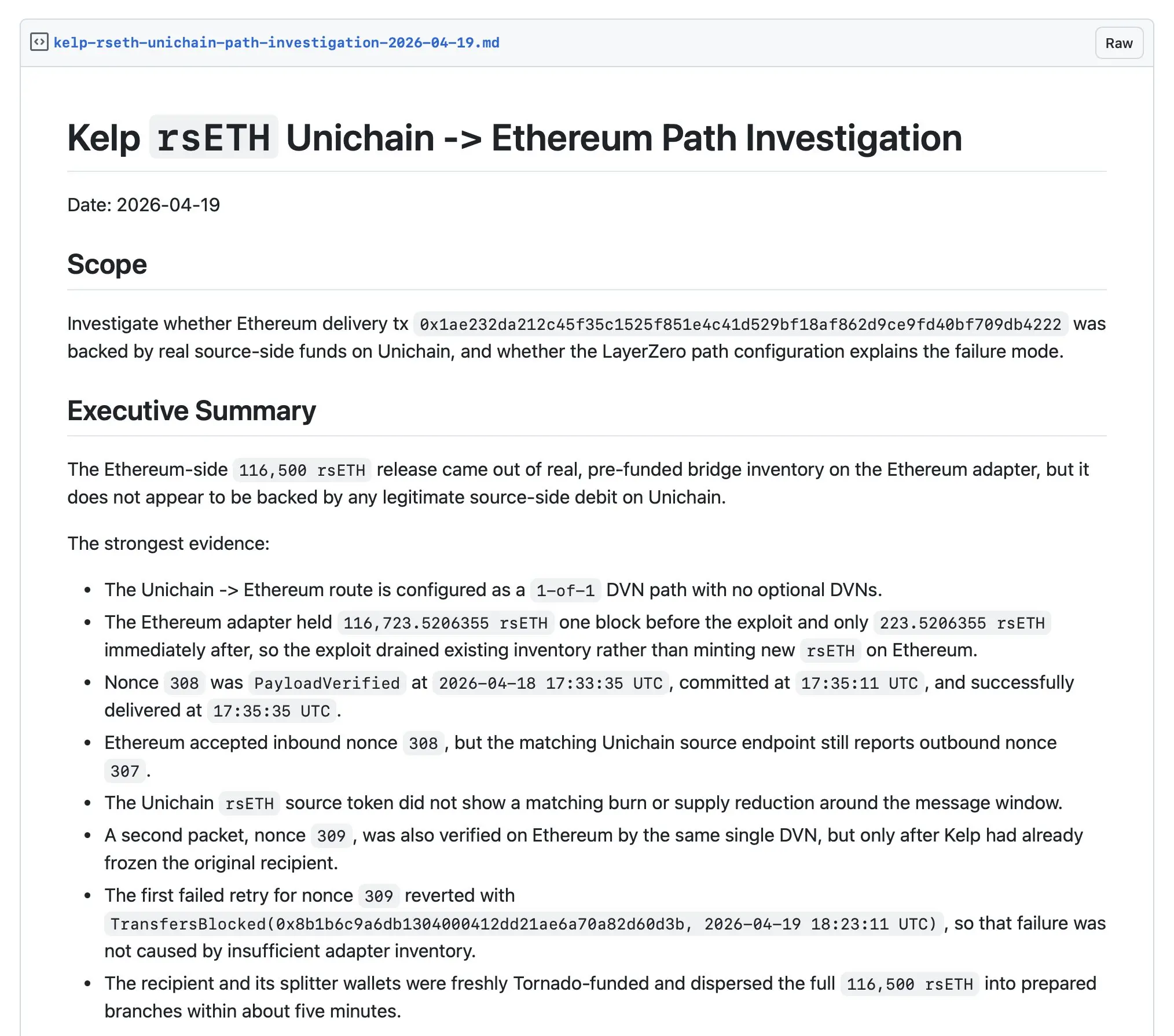
On Saturday, April 18, 2026, LayerZero bridge-related infrastructure associated with Kelp DAO was attacked. According to disclosures by blockchain security firm PeckShield, Aave locked the relevant market one hour earlier, and on-chain a transaction appeared showing 116,500 rsETH (at the time worth about $291 million) flowing into a new wallet.
Blockchain researcher Stacy Muur analyzed on X that this attack exploited a single point of failure: the attacker sent a “fake” message that prompted the Kelp DAO bridge to release rsETH on Ethereum, while not removing the corresponding amount of tokens from the Ethereum L2 network Unichain. Francesco Andreoli, Head of Developer Relations at Consensys and MetaMask, explained in an X post that the attacker did not directly transfer the stolen rsETH; instead, they used it to borrow ordinary funds from Aave, causing “massive bad debt.” Kelp DAO subsequently announced on X that it has paused rsETH contracts on the Ethereum mainnet and multiple L2 scaling networks.
Aave Liquidity Crisis: Data and Market Reaction
According to analysis published by on-chain analyst Yu Yan on April 20, 2026, since the attack occurred, deposits on the Aave platform fell from $45.8 billion to $35.7 billion, with outflows of about $10.1 billion; of that, stablecoin outflows were $4.5 billion. Aave’s stablecoin deposit interest rate remained at 13.4% for an entire day. Aavescan data shows that the attacker’s actions on Aave pushed the utilization rate of the core lending pool to 100%. Users who had previously deposited ETH and wETH had virtually no liquidity they could withdraw.
On X, DeFiLlama co-founder 0xngmi said that, as of early Sunday morning, Aave’s net withdrawals had reached $6.2 billion. Monetsupply.eth, alias strategy lead at Spark, pointed out in an X post that users borrowing against stablecoin collateral shows “negative secondary effects.” According to CoinGecko data, AAVE governance tokens fell to $90.13 on Sunday, down 16% from the previous day. In the same period, ETH fell 2% to $2,300. Tron founder Justin Sun also posted on X to address the attacker, asking “how much do you want?” and said the attack was not worth the damage inflicted on Aave and Kelp DAO.
Frequently Asked Questions
Which functions did the Reserve Protocol pause? Is redemption affected?
According to Reserve Protocol’s April 20, 2026 announcement on X, the scope of the pause includes eUSD minting, USD3 minting, rebalancing, and RSR redemption (unlock). The redemption feature remains normally open. ETH+ and bsdETH have zero risk assessment because they do not include rsETH collateral.
What are the loss amount and attack mechanism of the Kelp DAO rsETH attack?
According to PeckShield’s on-chain data, the attack involved 116,500 rsETH (worth about $291 million). Stacy Muur’s analysis on X indicated that the attacker sent a fake message via a single point of failure in the LayerZero bridge, released rsETH on Ethereum without corresponding burn, and used it to generate bad debt in Aave.
What data shows the impact of this attack on Aave’s liquidity?
According to Yu Yan’s analysis and Aavescan data, the utilization rate of Aave’s core lending pool reached 100% at one point; deposits fell from $45.8 billion to $35.7 billion, with outflows of about $10.1 billion. CoinGecko data shows that AAVE governance tokens dropped 16% on Sunday to $90.13.
Related Articles
Kelp DAO Hack Attributed to Lazarus Group; eth.limo Domain Hijacked via Social Engineering
DeFi Hack Triggers $9 Billion in Outflows from Aave as Stolen Tokens Used as Collateral
Ethereum Phishing Attack Drains $585K From Four Users, Single Victim Loses $221K WBTC
Pay attention to the signed content! Vercel is hit with ransomware demanding $2 million, and crypto protocol frontend security raises a red flag
KelpDAO Loses $290M in Lazarus Group LayerZero Attack
LayerZero responds to Kelp DAO’s 292 million incident: it indicates that Kelp set up a custom 1-of-1 DVN configuration, and the attacker was North Korea’s Lazarus.