AI code failure: Stop idolizing AI; Claude's coding caused a DeFi platform to lose $1.78 million
Author: ChainAnalysis Crypto Laboratory
1. Background: Oracle Configuration Hidden Risks
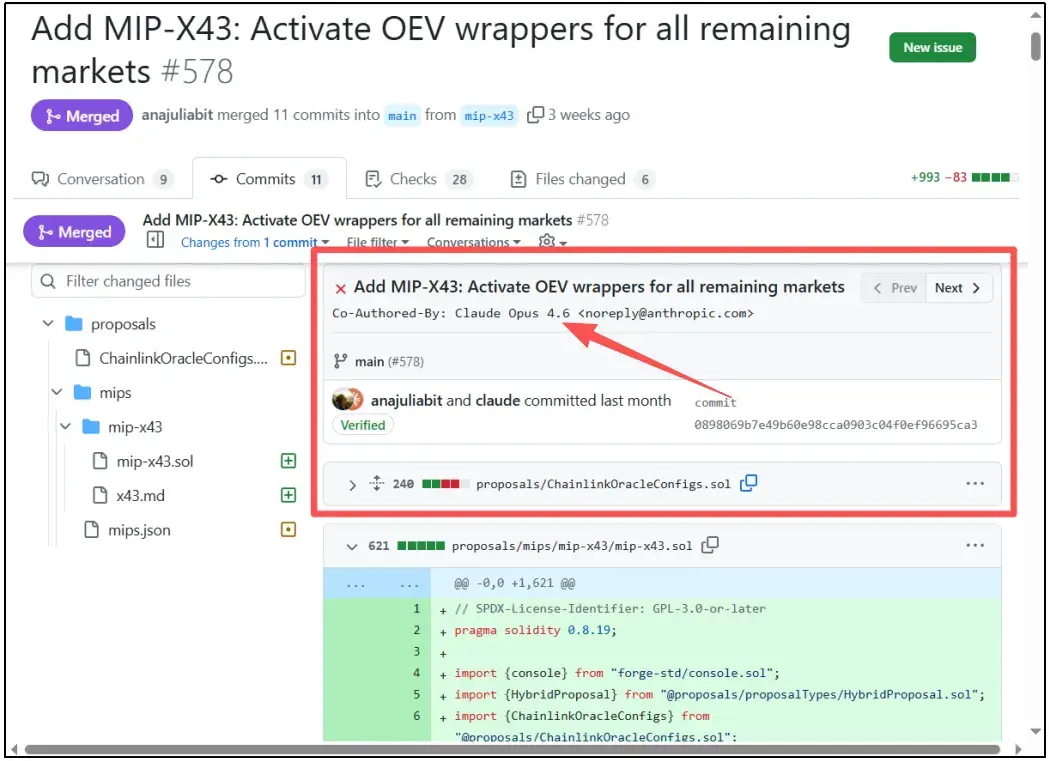
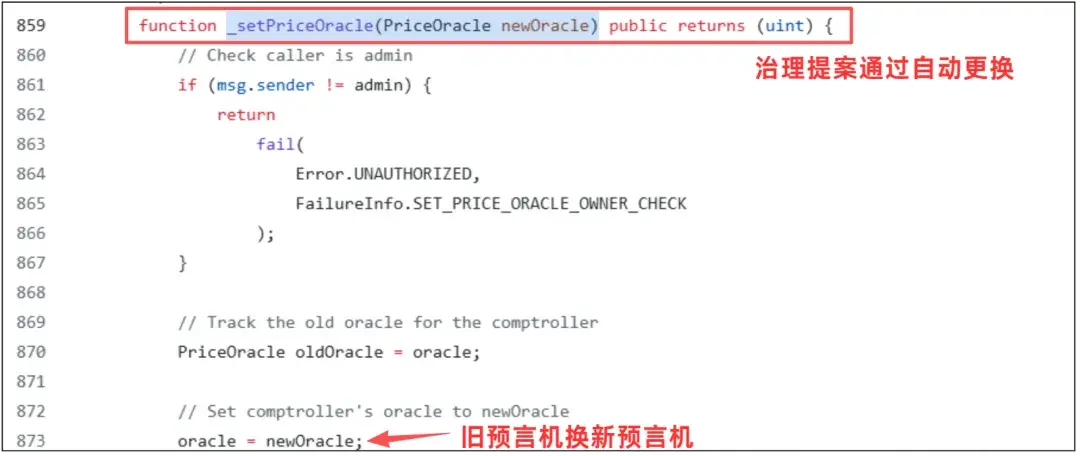
The incident began with a governance proposal (MIP-X43), which enabled a new Chainlink oracle configuration on Moonwell markets on Base and Optimism networks. (Note: An oracle is a tool that fetches real-time data before submitting it to the blockchain.)
In lending protocols like Moonwell, users deposit assets such as cbETH as collateral to borrow other tokens. If the market drops and the collateral value falls below the debt, automated bots will liquidate the position (the user’s total funds), repay the debt, and seize the collateral at a discount.
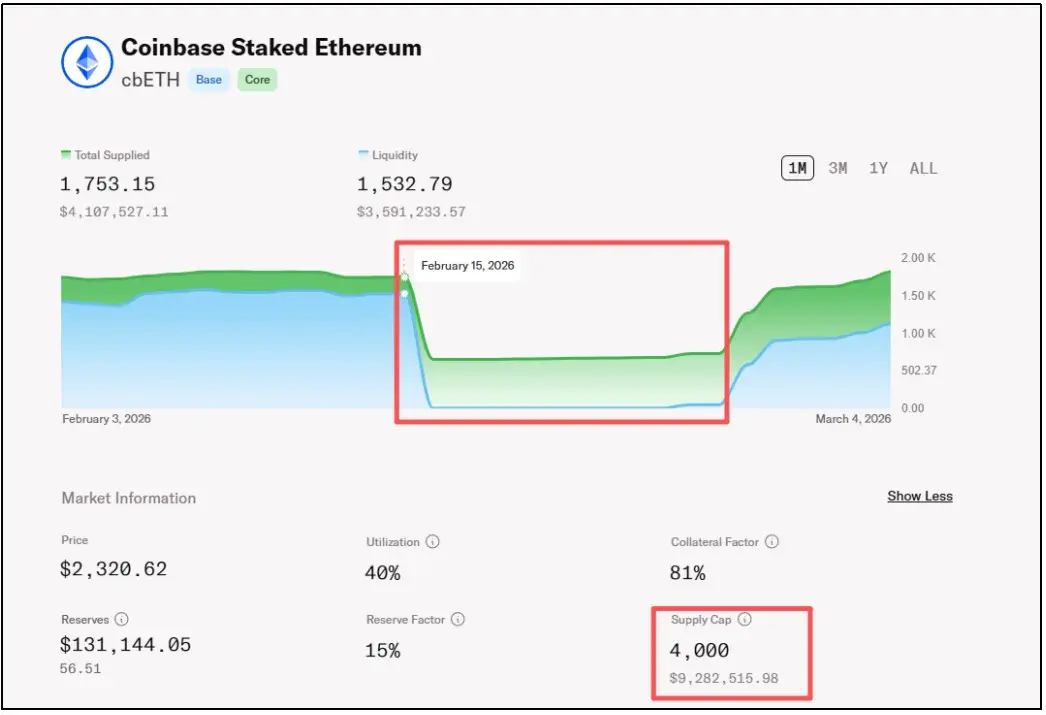
Before the event, Moonwell’s cbETH market had large funds and high collateralization, but the oracle testing was insufficient, missing a multiplication step, which caused severe price errors and sharply increased risk.
2. Analysis: AI Mistakenly Wrote a Piece of Code
This incident is the industry’s first on-chain security breach caused by Vibe Coding (AI-assisted coding), centered on a low-level yet fatal oracle configuration bug.
1. Cause of the vulnerability
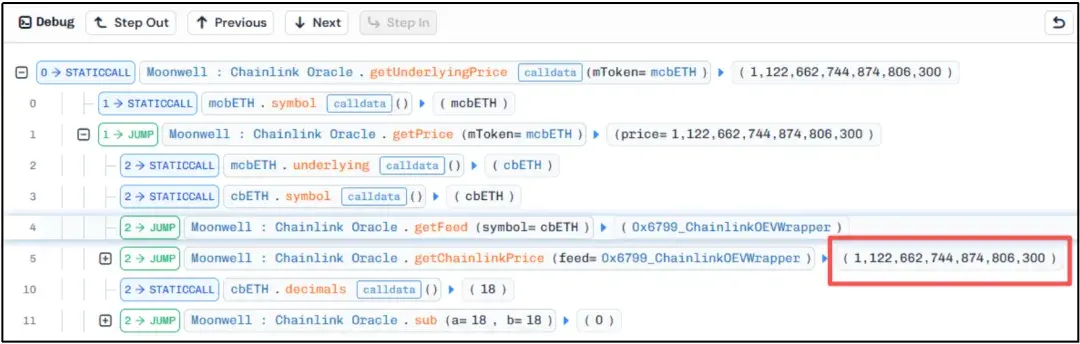
The root cause was an incorrect valuation of cbETH assets by the oracle. cbETH is a highly liquid staked token whose value includes accumulated staking rewards. Normally, 1 cbETH can be exchanged for about 1.12 ETH.

Therefore, the correct USD price calculation should be:
cbETH USD Price = (cbETH to ETH exchange rate) × (ETH USD price)
For example: If 1 cbETH ≈ 1.12 ETH, and 1 ETH ≈ $2200, then the true value of 1 cbETH should be about $2464.
However, in the code generated by AI tool Claude, due to lack of proper logical validation, the code directly pointed the cbETH price source to cbETHETH_ORACLE. This data source only provides the exchange rate (1.12), not the USD price of ETH.
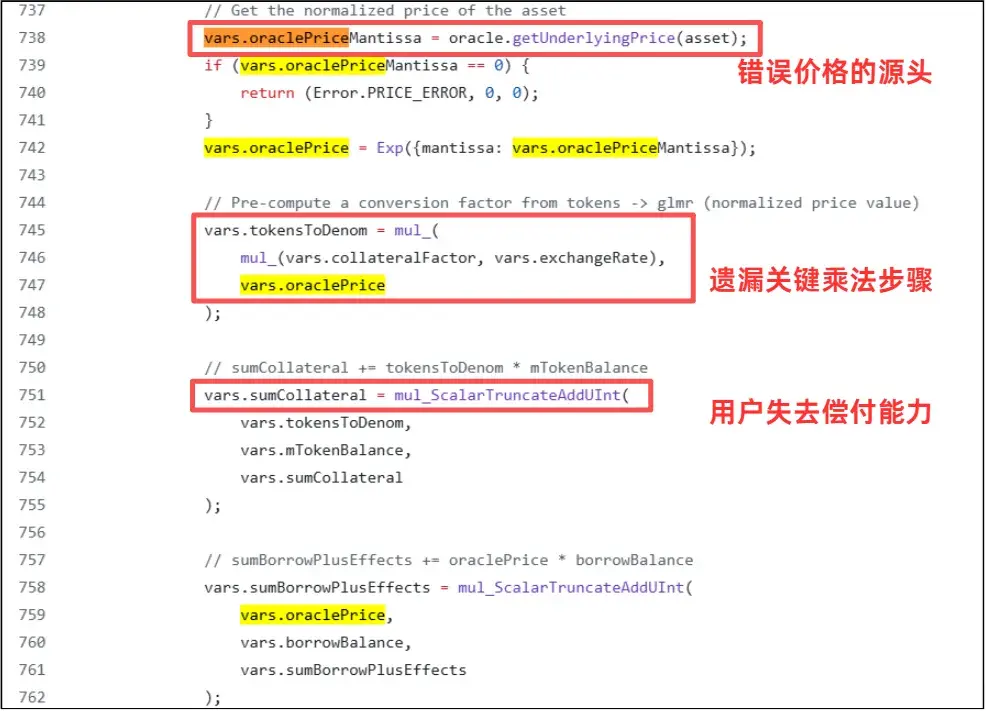
This omission of the critical multiplication step caused the program to treat the “exchange rate” as the “USD value.” An asset worth over $2400 was incorrectly marked as $1.12, undervaluing it by over 99.9%, with a price difference of nearly 2000 times.
2. Attack restitution
The severe underestimation of assets led the system to mistakenly consider many normal users’ collateral positions as “under-collateralized.” The exploitation process was highly efficient and automated:
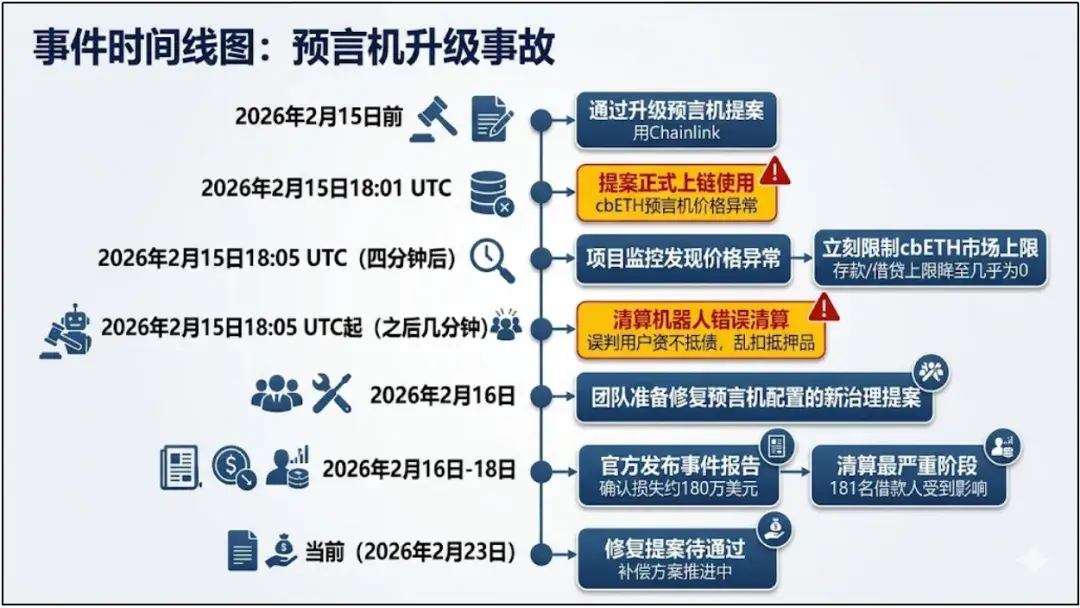
On February 16, 2026, at 2:01 AM UTC+8: MIP-X43 proposal was executed, activating the misconfigured cbETH oracle on Base.
On-chain liquidation bots monitored profit opportunities, quickly borrowing small amounts of USDC via flash loans at minimal cost to repay debt (since the system believed 1 cbETH was worth just over $1), thus gaining liquidation rights.

After seizing high-value cbETH collateral, the bots immediately sold it on DEX at market prices for profit. Multiple bots cycled rapidly within minutes, collectively seizing 1,096.317 cbETH.
This attack was not a premeditated hack but the result of liquidation bots executing absurd code. Since there was no traditional “thief,” where did the $1.78 million vanish to? The answer depends on the subsequent fund flow.
3. Fund Flow: No Hacker, Only Arbitrageurs
Since there was no traditional hacker, where did the $1.78 million evaporate to?
Where did the money go?
Answer: To the behind-the-scenes arbitrageurs deploying the liquidation bots.
These bots are not spontaneous; they are written and deployed on-chain by real programmers or quant teams (MEV searchers). When the system, due to AI missing a multiplication sign, “legally undervalued” assets worth over $2400 as just over $1, the hunting bots instantly seized the opportunity.
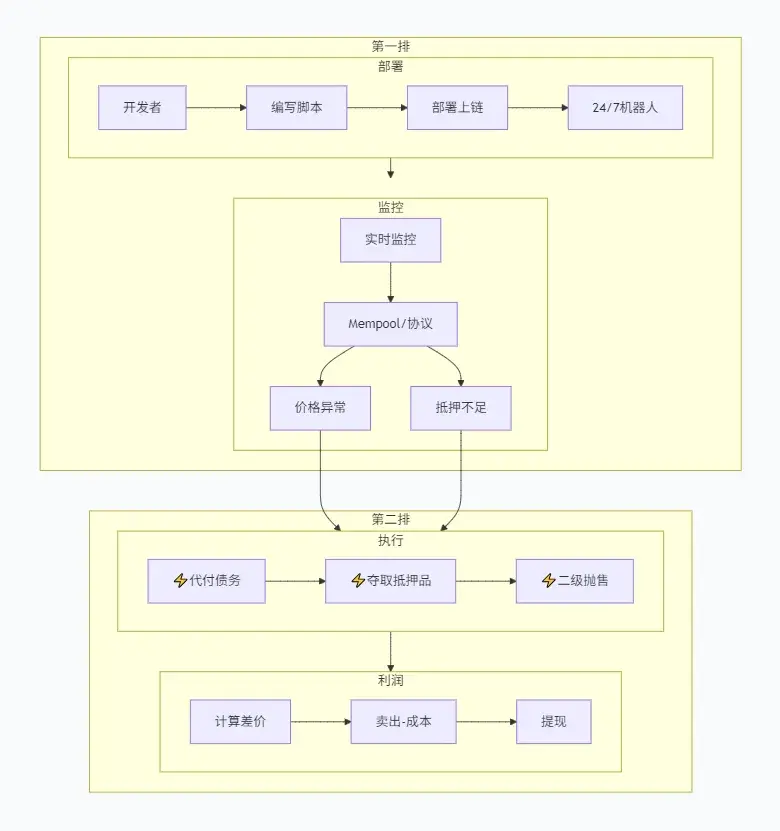
They automatically repaid the seemingly small debt, snatched high-value collateral, and resold it at market prices. Ultimately, the nearly $1.78 million profit flowed into the personal crypto wallets of the bot owners. They exploited the system bug to legally and compliantly withdraw millions.
In this incident, 11 assets suffered losses, with specific amounts as follows:
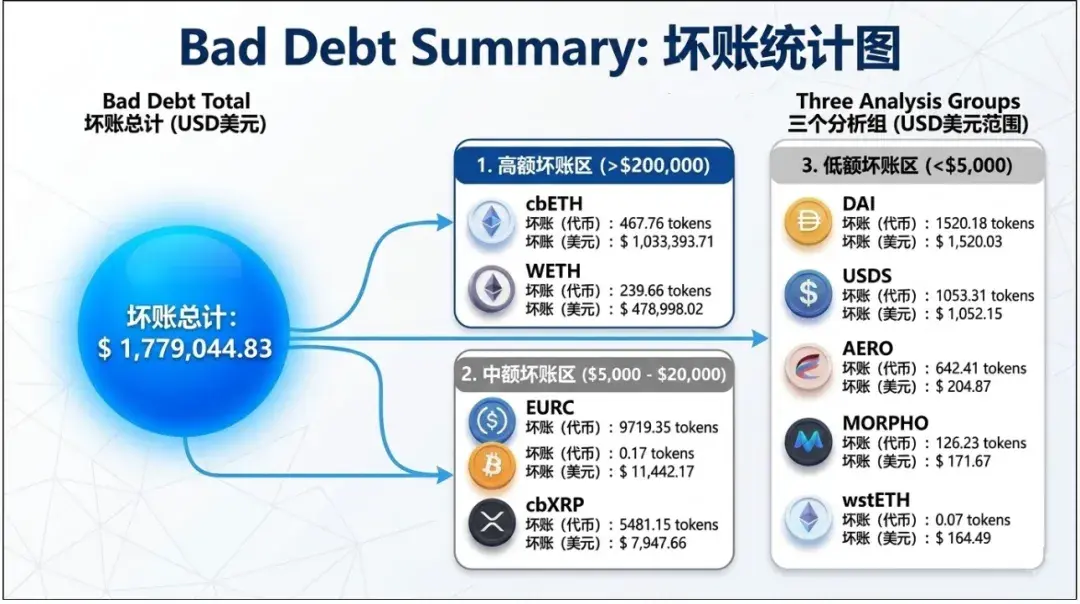
After the incident, Moonwell’s team quickly paused lending and liquidation functions, and rapidly submitted a new proposal to reconfigure the oracle parameters. To restore trust, the protocol used treasury funds to cover the $1.78 million bad debt and fully compensated the affected users.
4. AI in Charge: Efficiency or Security Risk?
After the event, most opinions blamed “Claude wrote the fatal bug,” but objectively, blaming AI for the $1.78 million loss is somewhat unfair.
This bug was nothing complex—just a simple configuration error: missing a multiplication.
Honestly, even a human programmer could make such a mistake.
The real issue was that the project’s review process was essentially nonexistent. Before launch, no one manually checked whether the “price logic” was reasonable. If you give correct instructions, AI can help you write clear, error-proof test cases.
The biggest lesson from this incident is not “AI can’t write code,” but that humans, in pursuit of speed, neglected the most critical review step.
No matter how good or fast AI is, it has no concept of real money and cannot be held responsible. AI can never replace humans; it’s just a powerful tool. Humans must use AI, not let AI call the shots.
5. Final Words: When AI Writes Code, Humans Must Stay Vigilant
The Moonwell incident is not complicated—no top hackers, no advanced exploits, not even complex attacks. It was simply an AI coding error, overlooked by humans.
But in the blockchain world, a single code oversight can mean millions of dollars in real assets. In DeFi, code is law; once written on-chain, it’s executed without hesitation. As more projects rely on “Vibe Coding,” code audits and risk controls should become the last line of defense.
Technology can become more automated, but security must never be automated.