Quantum Computing and Bitcoin: Real Risks, Technological Limits, and Response Strategies as of 2026
What Is Quantum Computing
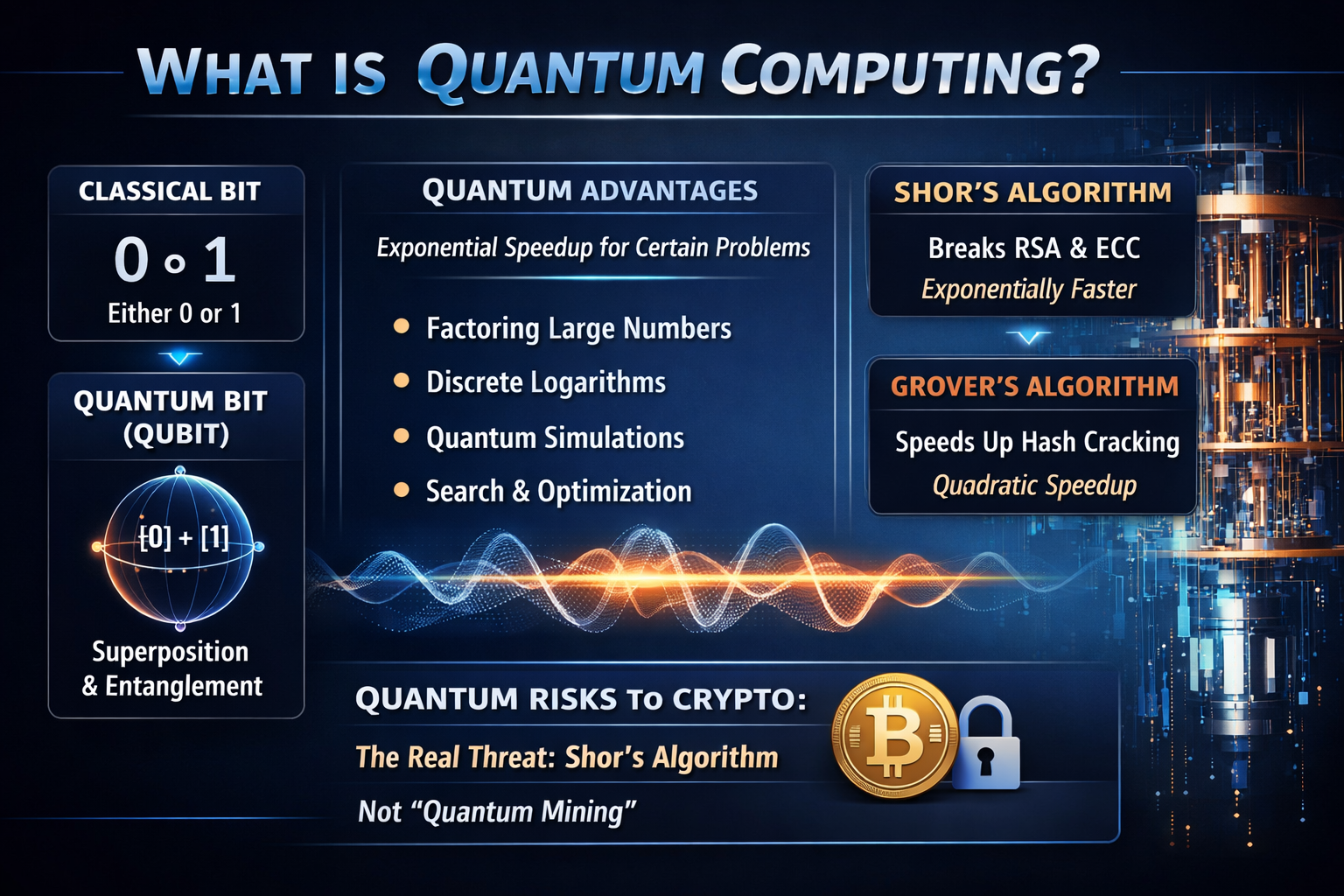
Quantum computing is an information processing paradigm grounded in the principles of quantum mechanics. Unlike traditional computers that use bits—each representing either 0 or 1—quantum computers operate with qubits, which can exist in superposition and leverage entanglement and interference, enabling problem-solving approaches fundamentally distinct from classical computation.
The significance of quantum computing does not stem from its potential to replace all conventional computation, but from its ability to deliver exponential advantages for a select set of problems, primarily including:
-
Large integer factorization
-
Discrete logarithm computation
-
Quantum system simulation
-
Certain search and optimization challenges
For cryptography, two classes of algorithms are especially critical:
-
Shor’s algorithm: Capable of exponentially accelerating large integer factorization and elliptic curve discrete logarithm problems, posing a direct threat to public-key cryptosystems such as RSA and ECC.
-
Grover’s algorithm: Offers quadratic acceleration for hash-related problems, but it does not “instantly break” hash functions; instead, it effectively reduces security strength from 2^n to approximately 2^(n/2).
This distinction is essential. The primary quantum risk to Bitcoin arises from Shor’s algorithm—not from the frequently exaggerated notion of a “quantum mining machine.”
Why Quantum Computing Could Impact Bitcoin
Bitcoin’s security does not rely on the “encryption of asset content,” but rather on digital signatures to prove ownership. In practical terms, attackers are not attempting to “decrypt the blockchain,” but to deduce Private Keys from public information to forge legitimate transactions.
Two layers must be distinguished here:
-
Hash functions: Bitcoin employs hash primitives such as SHA-256 and RIPEMD-160. While quantum attacks do exert some pressure, these algorithms have not yet reached the point of being compromised.
-
Digital signatures: Bitcoin has historically relied on ECDSA, with many newer outputs utilizing Schnorr signatures. Both are based on the elliptic curve discrete logarithm problem, which is particularly susceptible to quantum computing.
Accordingly, the real impact of quantum computing on Bitcoin is not a question of “whether the blockchain will disappear,” but whether “control over certain addresses may be lost.”
Where Bitcoin Is Truly Exposed
From a technical standpoint, not all BTC are exposed to the same risks at the same time. The degree of risk depends on whether the Public Key has already been revealed.
Risks can be broadly categorized as follows:
-
Early outputs with long-exposed Public Keys: For example, early P2PK outputs. If sufficiently powerful fault-tolerant quantum computers are developed, these assets would theoretically be more vulnerable.
-
Assets exposed by address reuse or specific script designs: These risks can be mitigated through asset migration and Wallet strategy optimization.
-
Ordinary UTXOs whose full Public Keys have not yet been disclosed: These remain relatively secure in the short term, as attackers lack direct access to the necessary public information.
This is why the narrative that “quantum computing will make all Bitcoin worthless overnight” does not hold. The real issue is that the risk to certain assets will increase first, requiring proactive preparation from protocol and Wallet infrastructure.
Recent Developments in Quantum Computing
Quantum computing news has become more frequent in recent years, but it is crucial to distinguish between “scientific breakthroughs” and “practical attacks.”
As of March 2026, Google Quantum AI published the paper “Securing Elliptic Curve Cryptocurrencies against Quantum Vulnerabilities: Resource Estimates and Mitigations,” further reducing the theoretical resources needed to break 256-bit ECC. Under specific superconducting hardware assumptions, the paper projects “fewer than 500,000 physical qubits and runtime measured in minutes.” While this demonstrates research progress, it does not indicate the existence of real-world, wallet-level devices capable of attacking Bitcoin.
Other noteworthy developments include:
-
December 2024: Google introduces the Willow chip, marking major advances in quantum error correction.
-
August 13, 2024: NIST officially releases the first post-quantum cryptographic standards, including ML-KEM, ML-DSA, and SLH-DSA.
-
From 2025 to 2026: Bitcoin Optech continues to monitor BIP-360, P2TSH, SLH-DSA optimizations, and hash-based signature schemes, signaling that the Bitcoin developer community has formally incorporated quantum resistance into ongoing discussions.
Collectively, these signals indicate that the threat is not “already here,” but the engineering preparation phase is underway.
Potential Real-World Impacts on Bitcoin
Should sufficiently powerful fault-tolerant quantum computers become a reality, Bitcoin could face several impacts:
-
Old coins with exposed Public Keys could be vulnerable to theft
-
Wallets, exchanges, and custodians would need to migrate to new signature systems
-
On-chain signature sizes, verification costs, and script design may need to be restructured
-
Legacy expansion schemes that rely on Public Key exposure would require a reassessment of their security models
Two frequently overlooked facts should also be emphasized:
-
“Quantum mining replacing ASICs” is currently not feasible. The theoretical acceleration Grover’s algorithm provides for hash searches is insufficient to disrupt existing Mining Machines, given real-world energy consumption, error correction, and hardware overhead.
-
Bitcoin is not incapable of upgrades. SegWit and Taproot have already shown that, while upgrades may be slow, Bitcoin is not static. The true challenge lies in social coordination costs, not protocol immobility.
The Direction of the Bitcoin Community
Rather than claiming that “Bitcoin is already quantum-resistant,” the more practical approach is phased advancement.
A realistic roadmap includes:
-
Prioritizing the reduction of unnecessary Public Key exposure: Wallets should avoid address reuse and adopt more Conservative receiving and migration strategies.
-
Introducing transitional solutions at the script and address layers: For example, the ongoing discussions around BIP-360 and its evolution are essentially about reserving protocol space for quantum-resistant signature verification.
-
Evaluating the on-chain costs of post-quantum signatures: Post-quantum solutions typically increase the size of Public Keys, signatures, or state management overhead, requiring a balance between security, verifiability, and block space.
-
Building cryptographic agility: Truly robust systems should not permanently bind themselves to a single signature assumption.
This is why the quantum resistance debate is not merely about “defending against quantum,” but also serves as a stress test for the upgradability of Bitcoin’s cryptographic infrastructure.
How to Objectively Assess the Situation
From both investment and technical perspectives, two extremes should be avoided:
-
Interpreting every quantum-related research paper as “the end of Bitcoin”
-
Asserting that, since no commercial attacks have occurred, “there’s nothing to worry about for decades”
A more prudent perspective is:
-
In the short term, quantum computing is not yet a direct factor affecting Bitcoin at the transaction level.
-
In the medium to long term, it is already a genuine issue that must be considered in protocol design, Wallet architecture, and custodial security.
-
For Bitcoin, the real risk is not an abrupt quantum “break,” but the possibility that, during a foreseeable preparation window, the community misses the opportunity for timely upgrades due to controversy, delays, or underestimation.
Quantum computing is not an immediate catastrophe, but it is likely to become one of the most significant external factors in cryptography over the coming decade or more. For Bitcoin, the most professional approach is neither panic nor denial, but to proactively treat it as a long-term, manageable, and engineerable risk.
Related Articles

In-depth Explanation of Yala: Building a Modular DeFi Yield Aggregator with $YU Stablecoin as a Medium

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape


