Bing AI Search Results Allegedly Poisoned: Hackers Distribute Fake OpenClaw Installer to Steal Crypto Assets
Event Overview: Bing AI Search Results Suspected of Poisoning
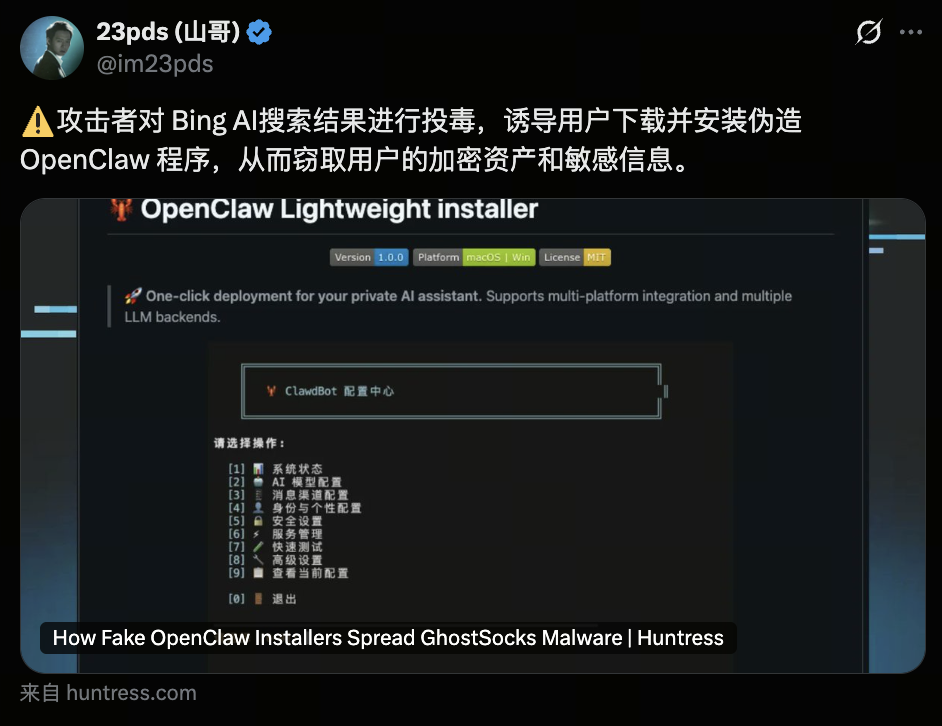 Image source: https://x.com/im23pds/status/2031163246783410581
Image source: https://x.com/im23pds/status/2031163246783410581
In March 2026, the head of security at blockchain security firm SlowMist issued a public alert, warning that attackers may have manipulated Bing AI's search results using "search poisoning" tactics. These actors lured users into downloading a counterfeit OpenClaw program, stealing crypto assets and sensitive information.
"Search poisoning" refers to attackers crafting specific websites or repositories to boost their ranking in search engine results. When users look up relevant keywords, malicious sites can be promoted to the top, or even be cited directly by AI-powered search results.
In this case, searching for keywords like “OpenClaw Windows” prompted Bing AI to recommend a fraudulent GitHub repository as the download source. After running the installer, some users' devices were infected with information-stealing malware.
Security researchers later confirmed that the malicious repository and installer had been removed, but the incident triggered widespread industry debate about AI search security and crypto asset protection.
What Is OpenClaw? Why Is It Targeted?
 Image source: OpenClaw Official Site
Image source: OpenClaw Official Site
OpenClaw is a recently popular open-source tool in the AI agent and automation development community, mainly used for building AI agents, automating tasks, and creating developer toolchains.
As AI agent and automation development frameworks rapidly evolve, user adoption of such tools is surging.
This quickly expanding developer ecosystem is an attractive target for attackers, for several reasons:
- Developers trust open-source repositories: Developers are accustomed to downloading tools and code from GitHub.
- AI toolchains often require high-level permissions: Many AI tools need access to system files, API keys, or cloud credentials.
- Significant overlap with crypto users: AI developers, Web3 developers, and crypto investors are often the same individuals.
As a result, by distributing fake OpenClaw installers, attackers can directly target devices containing wallet private keys, trading accounts, or API keys.
Attack Mechanism: From Search Poisoning to Malware Distribution
GitHub Repository Spoofing and Abusing Community Trust
Researchers identified that attackers created a GitHub organization called “openclaw-installer” and uploaded what appeared to be legitimate repositories.
To increase credibility, they even copied portions of the real project’s source code, making the repository structure look authentic.
Given GitHub’s strong reputation in the developer community and the added weight of AI-powered recommendations, many users assumed the repository was official.
The attack unfolded as follows:
- User searches for OpenClaw via Bing AI
- AI recommends the malicious GitHub repository
- User downloads the fake installer
- Malicious code silently executes information-stealing operations
This attack leverages open-source ecosystem trust + AI search recommendations, greatly increasing its success rate.
Distinct Payloads for Windows and macOS
Researchers found that attackers crafted different payloads for each operating system.
Windows attack path:
- Distributes a counterfeit installer called OpenClaw_x64.exe
- On execution, launches the Vidar info-stealer in memory
- Simultaneously installs the GhostSocks trojan for remote control
macOS attack path:
- Provides bogus installation instructions
- Tricks users into running Bash commands in Terminal
- Downloads and installs Atomic Stealer malware
These malicious programs primarily steal:
- Browser passwords
- Crypto wallet keys
- SSH keys
- API tokens
- Telegram/Discord login credentials
Once obtained, attackers can quickly transfer the victim’s crypto assets.
AI Search and SEO Poisoning: The New Frontier for Cyber Attacks
While search poisoning isn’t new, the rise of AI search is amplifying its effects. Research shows attackers can manipulate web content, repository structures, or keywords to push malicious resources higher in search results.
AI search introduces additional risks:
- AI actively summarizes and recommends content
- Users are more likely to trust AI recommendations
- Recommended links may bypass traditional search filters
Security analysts point out that simply hosting malicious code in a seemingly legitimate GitHub repository can get it indexed and recommended by search engines.
As a result, the combination of AI search + open-source platforms is becoming a major new attack vector.
Impact on the Crypto Industry and Developer Ecosystem
This incident highlights three significant trends:
1. AI tools are now prime attack vectors
As AI agents and automation tools become mainstream, attackers are disguising malware as AI tools.
2. Open-source trust is being exploited
Platforms like GitHub and PyPI, while open and transparent, are also easily abused by attackers.
3. Crypto assets are prime targets
Stealer malware typically seeks:
- MetaMask
- Browser wallets
- Local wallet files
- API keys
Once stolen, these assets are rarely recoverable.
User Security Guide: How to Avoid Similar Attacks
As attack techniques grow more sophisticated, users should consider the following precautions:
1. Download software only from official sources
Don’t download tools directly from search results; always use the official GitHub or website.
2. Verify code repositories
Check for:
- Official verification
- Long-term commit history
- An active developer community
3. Check installer signatures
Many security-conscious projects provide SHA256 or GPG signatures.
4. Use dedicated devices for private key management
Never store high-value wallet private keys in your development environment.
5. Use hardware wallets
Even if your computer is compromised, hardware wallets offer strong additional protection.
Security Challenges and Future Trends in the AI Search Era
The Bing AI search poisoning incident demonstrates that AI search systems still struggle to reliably filter trustworthy content.
As AI search, AI agents, and automation tools become essential entry points to the internet, attackers are evolving their methods, including:
- AI search poisoning
- AI-generated content deception
- Malicious code in AI agent plugins
Looking ahead, platforms will need to bolster defenses by:
- Strengthening AI search result source verification mechanisms
- Implementing trust scoring for open-source repositories
- Enhancing automated malware detection
For users, in an era where AI tools and crypto assets are deeply integrated, security awareness will be the most important line of defense for protecting digital assets.
Related Articles

Arweave: Capturing Market Opportunity with AO Computer

The Upcoming AO Token: Potentially the Ultimate Solution for On-Chain AI Agents

False Chrome Extension Stealing Analysis

What is AIXBT by Virtuals? All You Need to Know About AIXBT

AI Agents in DeFi: Redefining Crypto as We Know It


